Tag: Relay architecture
-

Nostr Protocol: Architectures, Security, and Privacy
This paper analyzes Nostr’s relay-centric architecture, key management, and threat models, highlighting privacy limitations and proposing practical enhancements to bolster censorship resistance and anonymity.
-

Nostr Protocol Client: Architecture, Keys, and Privacy
Nostr clients combine a relay-based architecture with end-to-end cryptographic key management; this analysis assesses client design, key handling, privacy trade-offs, threat models, and mitigations to bolster censorship resistance.
-

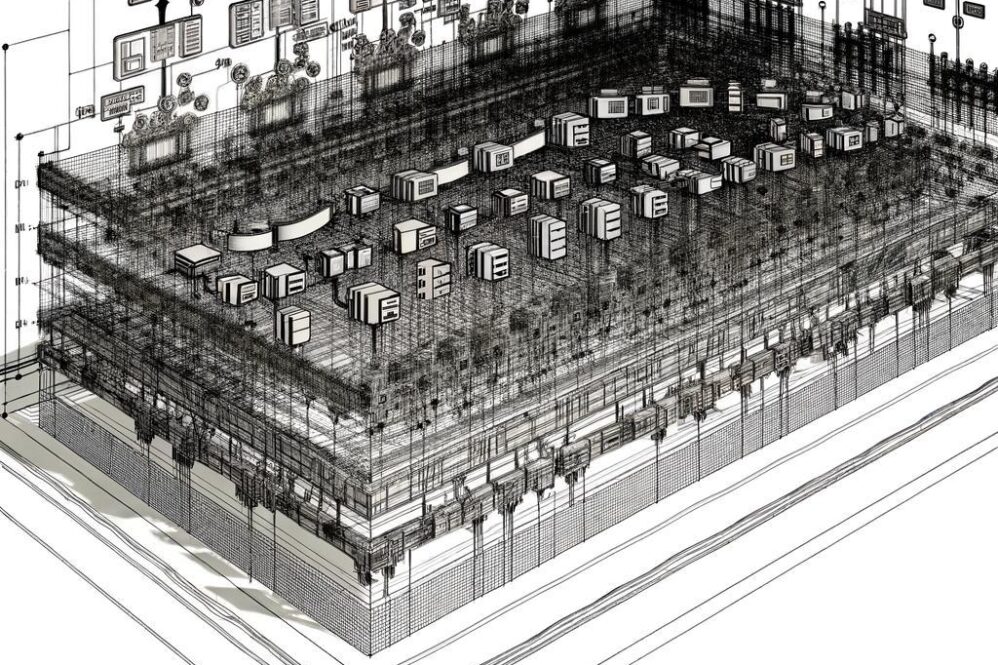
Understanding the Nostr Protocol Relay Architecture
This article examines Nostr relay architecture, detailing protocol design, message routing, concurrency handling, and performance under high load to inform optimization of decentralized communication systems.
-
Nostr Protocol Relays: Architecture, Function, and Limits
This study examines Nostr protocol relays, detailing their architecture, operational functions, and inherent limitations. It assesses performance, privacy trade-offs, and implications for decentralized communication.