Decentralized networks like Nostr open a vast spectrum of commercial possibilities by reshaping how facts is shared, verified, and monetized. Companies can leverage this protocol to create content distribution platforms that eliminate intermediaries, enabling creators to retain full control over their work and revenue streams. Additionally, enterprises can develop secure dialog tools that prioritize privacy and censorship resistance, a crucial advantage in today’s digital landscape.
Beyond information sharing,new business models can emerge around reputation systems and digital identities verified by cryptographic proofs inherent to Nostr’s framework. This innovation fosters trust in peer-to-peer marketplaces where users transact directly without centralized oversight. monetization strategies such as micropayments, subscription models, and tokenized incentives become feasible due to the protocol’s ability to support frictionless value exchange.
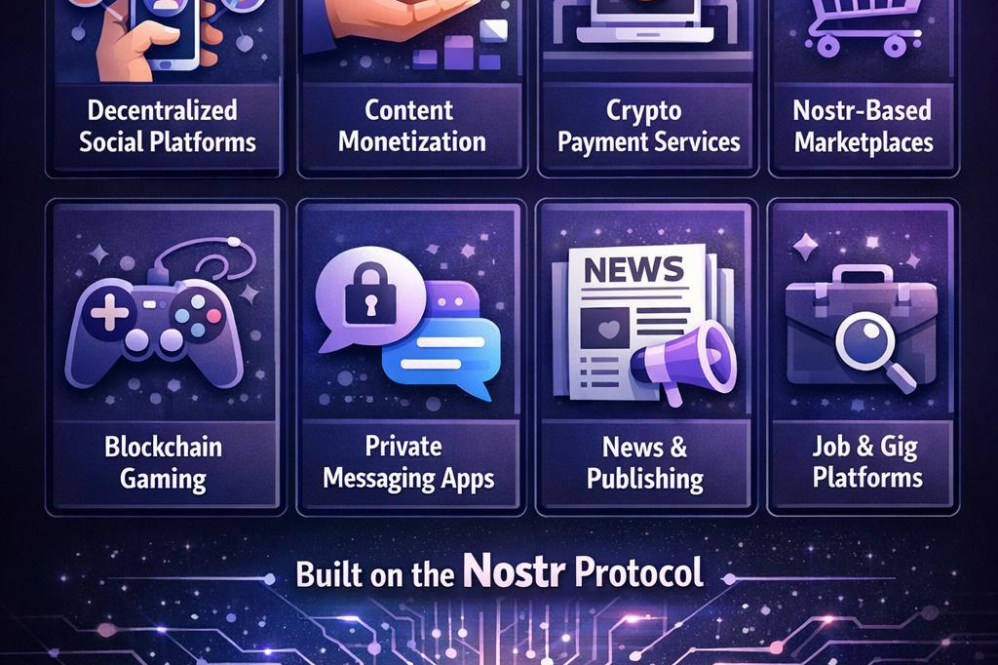
- Decentralized social networks with ad-free revenue structures
- Encrypted messaging services with zero data retention
- Peer-to-peer marketplaces backed by trustworthy digital IDs
- Event and ticketing platforms resistant to scalping and fraud
- Subscription and donation systems leveraging native value transfer
| Business type | Unique Value Proposition | Monetization |
|---|---|---|
| Social Media | Decentralized control, censorship resistance | Subscriptions, donations |
| Secure Messaging | End-to-end encryption without central servers | Premium features, enterprise licensing |
| marketplace | Trustless transactions, verified identities | Transaction fees, token ecosystem |
| Event Platforms | Anti-fraud ticketing, decentralized verification | Service fees, sponsored events |
Create your Nostr Profile