Understanding the Mechanics of Onion Routing: How It Works to Protect Your Privacy
Onion routing is a powerful technology designed to enhance online privacy by obscuring the user’s location and activity. The core mechanism involves the use of layered encryption, where data is encapsulated in multiple layers, akin to the layers of an onion. Each layer of encryption is removed at different nodes in the network, meaning that no single node knows both the origin and the destination of the data. This multi-layered approach significantly complicates the task of anyone trying to intercept or trace the data back to the user.
The routing process begins when a user initiates a connection to the internet. The user’s data is first encrypted and then sent through a series of randomly selected nodes, each operated by different individuals or organizations, often referred to as “onion routers.” As the data travels through this network, each node decrypts only enough information to know where to send the data next. This ensures that even if one node is compromised, it can only reveal limited information, keeping the entire communication chain secure. The nodes do not store information about the connections, further enhancing privacy.
Ultimately, this architecture offers a robust defense against various forms of surveillance and tracking. By anonymizing the user’s location and disguising their online actions, onion routing makes it incredibly challenging for third parties, such as advertisers or government entities, to monitor individual activities. As cyber threats become increasingly complex, understanding and utilizing technologies like onion routing becomes crucial for anyone who values their online privacy and security.
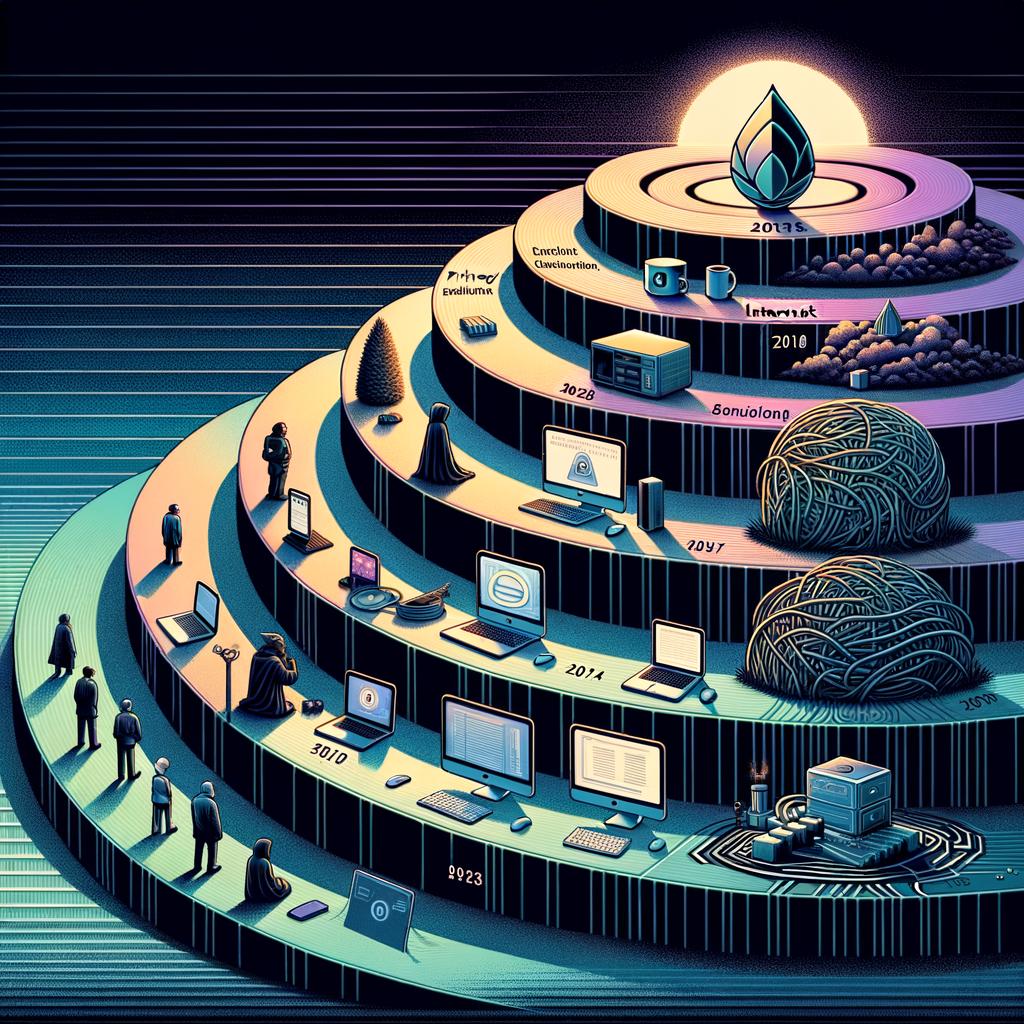
The Evolution of Online Anonymity: The Role of onion Routing in the Digital Age
Onion routing emerged in the late 1990s as a pioneering solution to the growing concerns over online privacy. Developed by the U.S. Naval Research Laboratory, the technology was initially intended to protect government communications. It’s innovative approach employs a system of layered encryption in which user data is wrapped in multiple layers, resembling the layers of an onion. Each layer is decrypted at successive nodes, making it exceedingly difficult to trace the origin of the data back to the user. This system effectively obscures not only the user’s identity but also their browsing activity from prying eyes.
As online tracking and surveillance measures have become increasingly sophisticated, onion routing has evolved to address new challenges in the realm of digital anonymity. Modern implementations,most notably the Tor (The Onion Router) network,expand on the original concept by enabling users to connect through a series of volunteer-operated servers. This decentralized structure further enhances anonymity, as no single node holds the complete information about the data being transmitted. Additionally,the rise of threats like data harvesting and invasive advertising practices has propelled onion routing into the spotlight as a viable alternative for privacy-conscious users.
The potential impact of onion routing on online behavior cannot be overstated. As digital rights advocates push back against invasive surveillance practices, tools like Tor demonstrate a commitment to safeguarding personal privacy. This shift is evident in the growing user base of onion routing services, particularly among activists, journalists, and those living under repressive regimes. By providing a means to bypass censorship and maintain anonymity,onion routing has not only changed the way we navigate the internet but has also sparked crucial discussions about the future of privacy in our increasingly interconnected world.
Best Practices for Using Onion Routing: Maximizing Your Security and Anonymity online
To ensure maximum security and anonymity while utilizing onion routing, it is crucial to adopt a cautious approach to your online activities. The first recommendation is to use verified and reputable onion routing software, such as Tor Browser, which is specifically designed to utilize the onion routing protocol effectively. it is also essential to keep your software updated to protect against known vulnerabilities. Always disable any features that may compromise your anonymity, such as scripts, plugins, and media players, as these can leak your IP address.
Another key practise involves being mindful of your online footprint. Users should refrain from logging into personal accounts, such as email or social media, while using onion routing, as this could reveal your identity or location. Additionally, it is prudent to avoid sharing any personal information on onion routing services, even if you believe the interaction is secure. Always ensure that your communications are encrypted, and use end-to-end encryption wherever possible to add an additional layer of security.
it is wise to understand the limitations of onion routing. While it provides significant anonymity, it does not protect you from all forms of surveillance. to enhance your security, consider using a reliable VPN in conjunction with onion routing. This can help obfuscate your internet traffic before it enters the onion network, adding an extra layer of privacy. Always be aware of the potential risks associated with browsing the darknet and exercise caution when accessing sites that may host illegal or harmful content.
onion routing emerges as a vital tool in the quest for online privacy,providing users with an effective means to navigate the web without compromising their anonymity. By utilizing a multi-layered encryption approach,onion routing cloaks user data in several layers,routing it through a network of nodes that obscures the origin of the information. This innovative technology empowers individuals to protect their digital footprint against pervasive surveillance and tracking, ensuring a more secure online experience.
As our digital lives continue to evolve, understanding and implementing tools like onion routing becomes increasingly crucial. The challenges posed by data breaches, government surveillance, and corporate tracking underscore the need for heightened privacy measures. By demystifying onion routing, we not only equip ourselves with the knowledge to safeguard our online activities but also contribute to a broader dialog on the importance of privacy in an interconnected world. As we move forward, let us remain vigilant and informed, embracing technologies that foster a more private and secure internet for all.