Nostr, by design, operates as a decentralized and censorship-resistant messaging protocol, emphasizing openness and verifiability.However,this architecture inherently challenges traditional encryption methods commonly used too secure private communications. Messages broadcasted on Nostr relays are publicly visible, raising questions about whether and how encryption can be effectively implemented without compromising teh network’s transparency and trustless nature.
despite these challenges, several cryptographic strategies can be employed to encrypt Nostr messages:
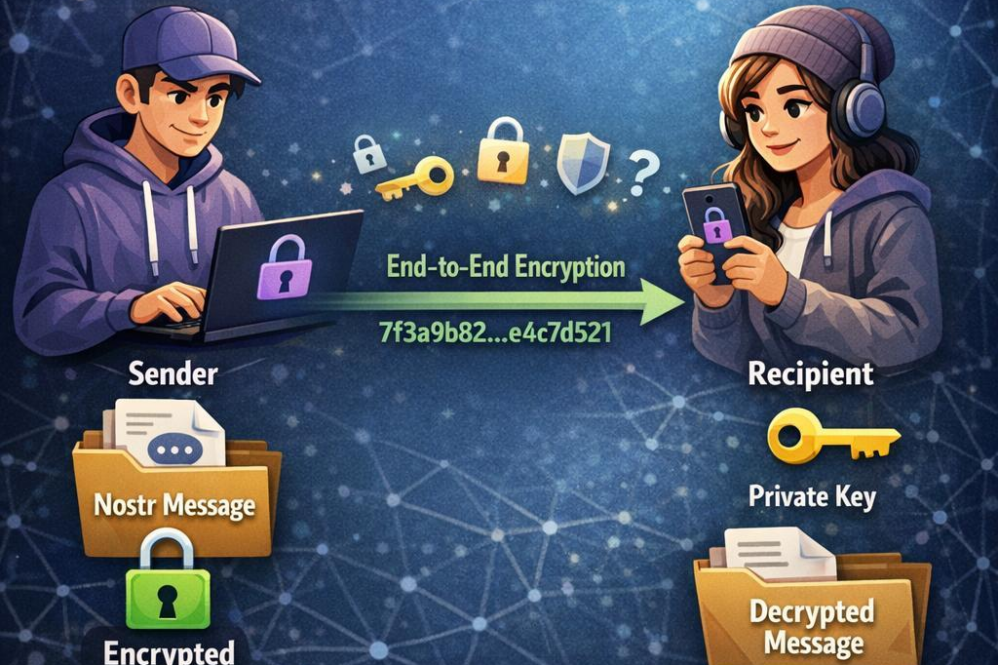
- End-to-End encryption (E2EE): users can encrypt the content locally before publishing, ensuring that only intended recipients with the decryption key can read the messages.
- Public-Key Cryptography: Given that each nostr user has a unique key pair, leveraging asymmetric encryption allows secure message exchange without exposing keys publicly.
- Hybrid Encryption Schemes: Combining symmetric encryption for the message payload with asymmetric encryption for key exchange optimizes both security and efficiency.
The table below summarizes the encryption options relative to Nostr’s architecture:
| Encryption Method | Advantages | Considerations |
|---|---|---|
| End-to-End Encryption | Confidentiality assured only to sender and receiver | Requires key distribution among users |
| Public-Key Cryptography | Secure key exchange without prior contact | Relays see ciphertext only, preserving privacy |
| Hybrid Encryption | Balances speed and security effectively | Complex implementation compared to pure methods |
while Nostr messages are not encrypted by default, adopting cryptographic patterns tailored to its protocol can robustly secure communications without undermining decentralization. This nuanced approach allows users to maintain control over privacy in an otherwise open habitat.
Create your Nostr Profile